Job Roles of Vulnerability Analyst and How Do They Work?
Last Updated : 04 Jul, 2024
 33.52K
33.52K

Introduction
When we talk about cyberspace, cyber attacks automatically become the associated topic of discussion. Put simply, with the growing convenience of the cyber world, hacking incidents are also rising at an equal and alarming pace. Despite the implementation of advanced threat detection systems, there has been a 20% increase in organisational cyber breaches. These menacing attacks are mostly abetted by undetected and unresolved security vulnerabilities in an organisation’s network and applications. Thus, organisations are finally waking up to the need of rigorous vulnerability analysis and penetration testing. This wake-up call has further led to a growing demand for qualified and proficient vulnerability analysts. As reported by a leading job hunt portal, the average pay of data analysts in India ranges between ₹5.0 LPA – ₹10 LPA.
Want to command your desirable package as a vulnerability tester? Explore the nitty-gritty of this profession and the professionals in this in-depth guide.
Who is a vulnerability analyst?
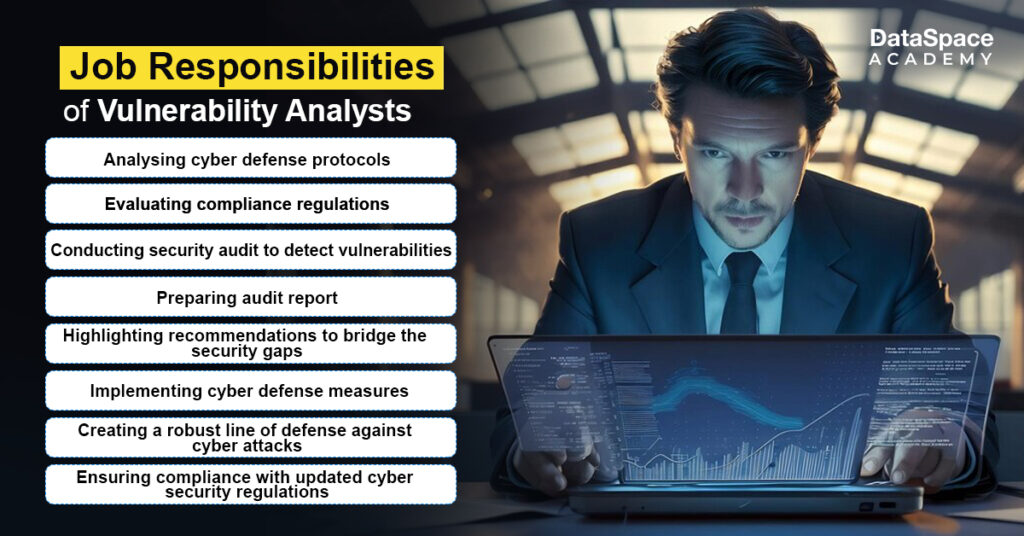
A vulnerability analyst is a cybersecurity professional who is shouldered with the responsibilities of analysis of vulnerability of an organisation’s network and applications.
They check vulnerability of a website or an application by identifying potential system flaws that the threat actors can exploit. Based on the security audit report, vulnerability analysts recommend measures to bolster the security posture to protect the organisation from both internal and external threats.
How do vulnerability analysts work?
A vulnerability analyst has to follow and execute an extensive checklist of responsibilities to ensure a robust security infrastructure. Let’s explore their work mechanism step by step:
- Craft a blueprint: Vulnerability assessment in cyber security isn’t an overnight process. It requires planning and a systematic process of conducting meetings, creating a threat model, and brainstorming with the security analysts & developers.
- Assess the outcomes: Some companies may implement vulnerability assessment as a regular mandate but outlining the outcomes before assessment is a must. This enables the analysts in effective assessment of the system therefore reducing the probability of breaches and recovery time.
- Assess the arsenal: Before proceeding with the audit, vulnerability analysts evaluate their vulnerability assessment tool kit to ensure they are well-equipped to detect even the most sophisticated loopholes.
- Running the vulnerability audit: While performing the assessment, a vulnerability analyst manually performs a set of detection techniques to filter out false positives. It helps the analysts to ensure a secure connected system and network through evidence collection during the review process.
- Draft a detailed report after each assessment: Performing vulnerability assessment provides valuable knowledge to the vulnerability professionals about the nature and impact of a threat. Creating a detailed report of the vulnerabilities, associated risks, and remedies is among the crucial responsibilities of a vulnerability analyst.
Consistent Learning is the Key
With new threats popping up over time and attacks getting more sophisticated- professional vulnerability analysts should keep on upgrading them with more advanced knowledge and skills. Besides obtaining professional certifications, they must invest quality time in self-learning from assessment reports to gear up for future risks.
Skills required to be a vulnerability analyst
To become a vulnerability analyst, a candidate or aspirant must qualify the following parameters:
- Must-Have Technical Skills:
- Knowledge in hardware and software systems
- Proficiency in various programming languages such as C, C++, PHP, Java, and so on
- Experience in Windows and Unix operating systems
- Familiarity with networking tools such as Nessus, RETINA, ACAS, and Gold Disk
- Proven expertise in scanning web applications
- Mastery in generating vulnerability management reports
- Experience in using various network vulnerability analysis tools like Nmap and Wireshark
- Gaining extensive knowledge in security frameworks like HIPPA, ISO 27001/27002, NIST, and SOX
- Excellent Soft Skills:
A vulnerability analyst must also invest considerable time in honing soft skills for effective assessment and operation as a part of the dedicated team. Their preferred list of soft skills includes:- Creative and analytical thinking
- Strong detail orientation
- Proactive problem-solving ability
- Robust verbal and written communication skills
Conclusion
Vulnerability Analysts are currently one among the most in-demand cybersecurity professionals around the globe. Considering the predictive statistics of organisational breaches, it won’t be wrong to claim that busy days are knocking for skilled security professionals. Plus, the lucrative pay and perks associated are attracting the aspirants to be a part of this thriving USD 181 billion industry. Here is your chance to upgrade your skills with DataSpace Academy’s highly acclaimed advanced penetration testing course and give wings to your dream.
 33.52K
33.52K




































































































