With the growing importance of network security and cloud migration among businesses, there is a spiking need for skilled network professionals in the market. All these factors have accelerated the importance of CCNA certification - the golden ticket for network professionals to unlock better opportunities. By becoming a CCNA-certified professional, you gain the confidence and qualifications to secure top-tier positions with competitive salaries.
Remember, the network framework is constantly evolving with emerging innovations and rapid cloud adoption. So never stop upskilling as this is your only gateway to staying job-relevant in the competitive job market. However, choosing a job-ready course that makes you an adaptable player in the dynamic network sphere is not easy. But not anymore. To steer your career in the right direction, we present a comprehensive CCNA certification roadmap. So, let’s dive in.
CCNA is a category of technical networking certification offered by Cisco. Designed especially for networking professionals, the certification validates a candidate’s ability to deploy, manage, and resolve issues and errors in enterprise networks. Upon completing this Certification, professionals gain a comprehensive understanding of networking concepts and hone their existing skills and expertise. Mastering the Cisco networking course is the key to limitless opportunities in your current job, promotions, and new job opportunities.
To enroll in the Cisco Certified Network Associate certification exam, you don’t need to necessarily have a degree or certification. However, Cisco recommends aspirants to have at least a year of experience as a network administrator or be familiar with the basics of networking fundamentals.
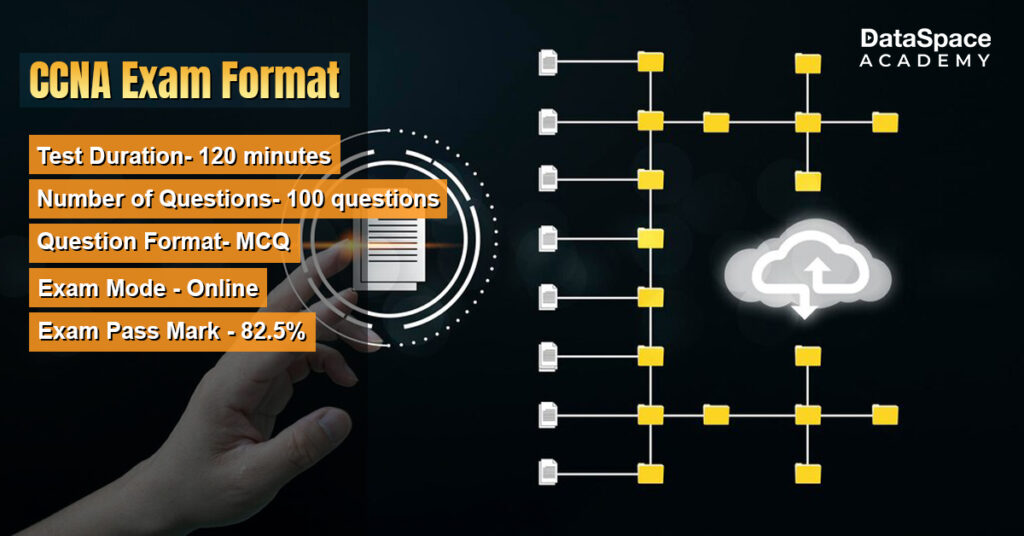
The CCNA certification exam is a 120-minute test, consisting of 100 questions. The featured questions are a mixed bag of multiple-choice, drag-and-drop, simulation, and performance-based. The exam is conducted online and an aspirant needs to score at least 825/1000. If you want to attempt the exam, you will have to pay a fee of $300 (INR 22,500 + tax). In case you are unable to qualify in the very first attempt, you can retake the exam after 14 days.
Interesting scoop: As per the latest employment report, CCNA certification is a commonly requested criterion for more than 18,500 job listings on LinkedIn.
Qualifying for CISCO network certification extends multiple advantages for your career:
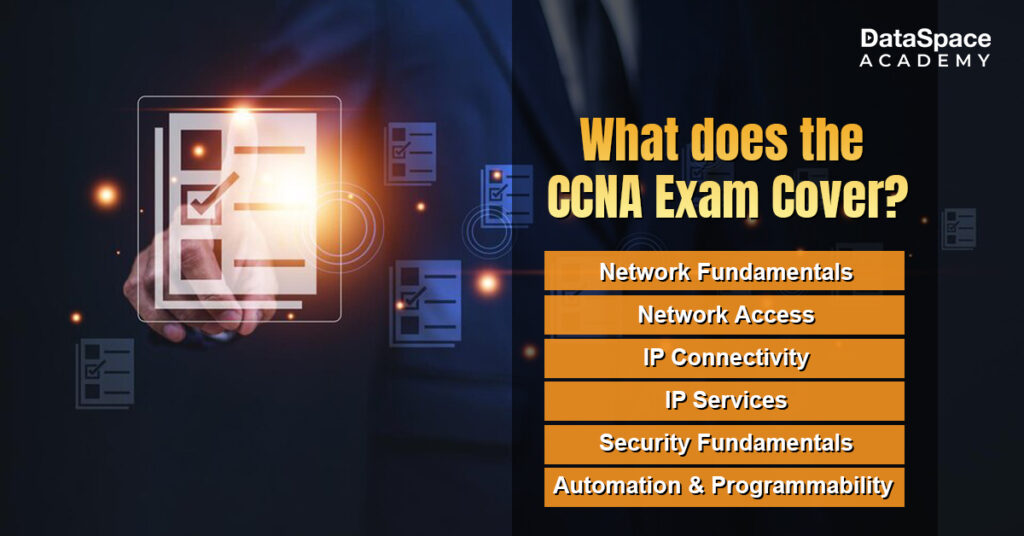
To attempt this exam, you need to know the exam breakdown, which is as follows:
You can easily ace your CCNA networking certification exam with the following tips:
One of the most challenging certifications for networking professionals, the CCNA exam demands rigorous study. The best tip is to sign up for a
CCNA training online course like the one offered by DataSpace Academy.
You have to find a course that is meticulously designed to help CCNA aspirants crack the Certification exam. The one offered by DataSpace Academy encompasses all the topics covered by the CCNA Certification, including practical training. You will receive expert-curated study materials from the Academy that will empower you to qualify for the exam at the very first attempt.
Upon completing CCNA, one can have the golden opportunity to apply for several diverse job roles like
The CCNA certification provides numerous benefits for aspiring network professionals, including a comprehensive understanding of networking fundamentals and increased job opportunities. Enrolling in a
CCNA training course with Dataspace Academy offers structured learning with expert instructors and interactive labs that enhance comprehension and practical skills. Additionally, the supportive community and resources provided by Dataspace Academy can help students succeed in their CCNA journey - ultimately leading to better career prospects and higher earning potential

 Upto 50% Off on All CoursesValid till 15/07/2025
Upto 50% Off on All CoursesValid till 15/07/2025
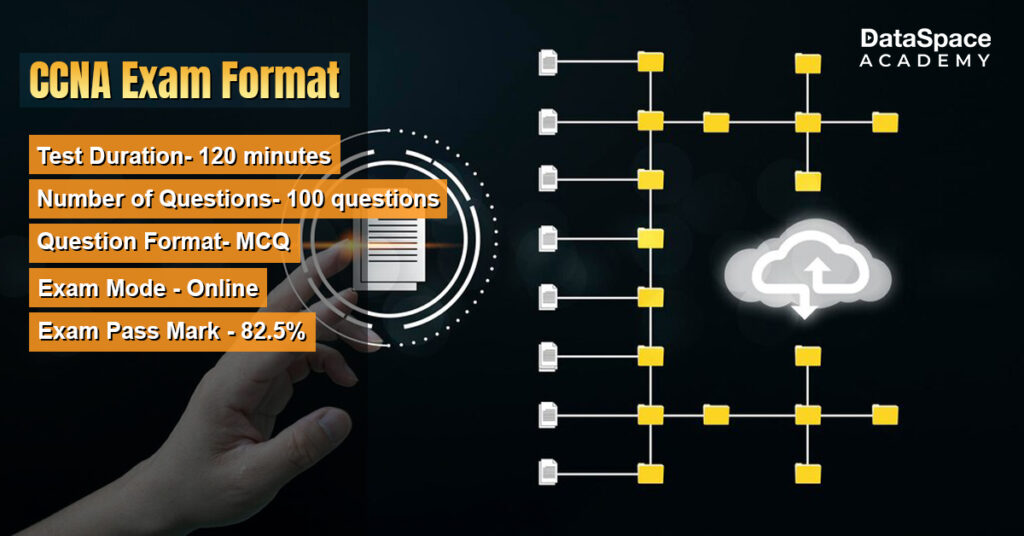
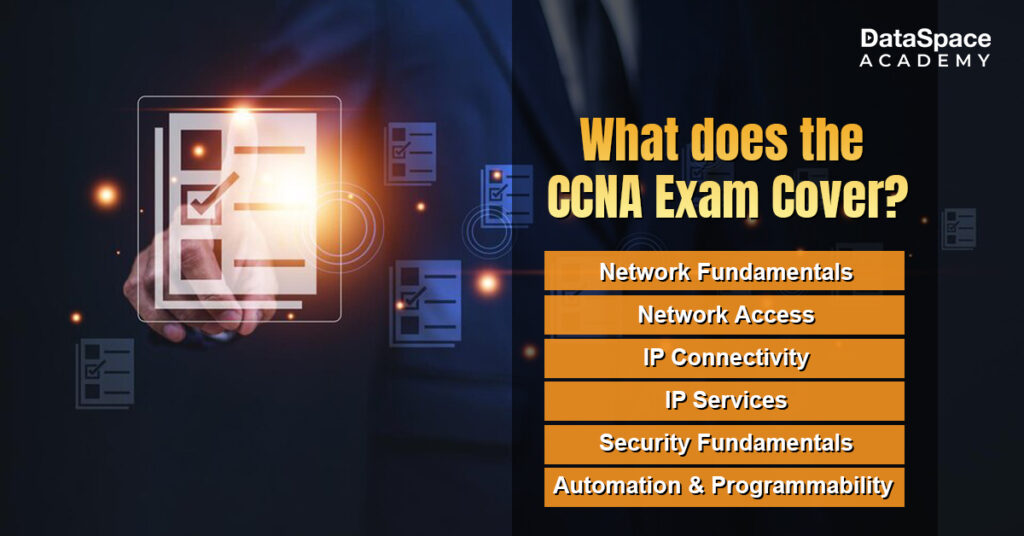 To attempt this exam, you need to know the exam breakdown, which is as follows:
To attempt this exam, you need to know the exam breakdown, which is as follows:
