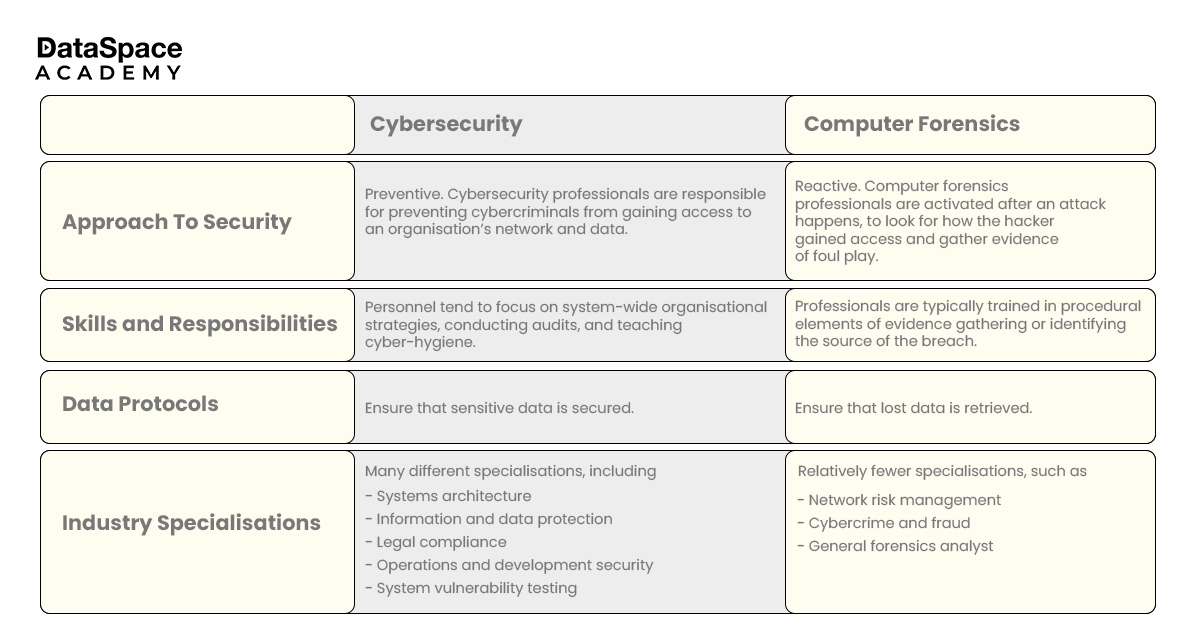
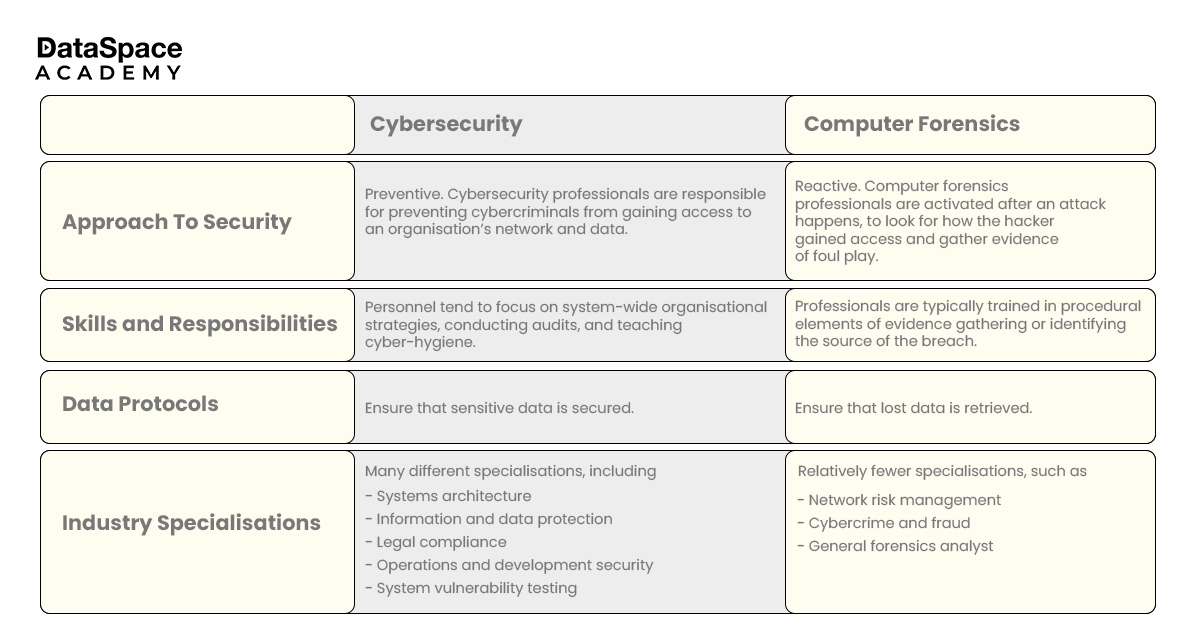
[br]The terms cybersecurity and digital forensics are often used interchangeably. But are they the same? While both are essential components of information technology, they serve distinct purposes.
While cybersecurity primarily focuses on protecting devices and systems from attackers, digital forensics uses investigative techniques and technology, to identify, collect, and store evidence from electronic devices.
In this blog, we deal with the key differences between cybersecurity and digital forensics, shedding light on their unique roles, methodologies, and why they are important today.
Cybersecurity is the method of protecting computer systems, networks, and data from theft, damage, or unauthorised access. Its primary objective is to maintain the confidentiality and integrity of the digital assets. Instead of being defensive, today most cybersecurity analyst focus on being proactive at protecting their systems (computers, smartphones, networks, and databases) from attack.
Here's a closer look at the core aspects of cybersecurity:
Digital forensics, on the other hand, is the process of collecting, analysing, preserving, and presenting digital evidence to resolve cybercrimes. Professionals use dedicated cybersecurity forensics tools to run their investigations.
Some of the distinct characteristics of digital forensics:
While cybersecurity and digital forensics have distinct roles, they are closely intertwined. You can say that they are two sides of the same coin, working together to secure the digital assets. Here's how they complement each other:
Cybersecurity and
cyber forensics work together to protect systems from attacks and investigate incidents. If a breach occurs, digital forensics teams use scientific techniques and technologies to collect and analyse electronic data to identify and mitigate cybercrime. They can also recover data and identify the culprit behind the crime.
Both cybersecurity and digital forensics are among the top job-generating domains. Among the top cybersecurity and digital forensics jobs here are the top ones:

Cybersecurity and digital forensics are in high-demand careers. Organisations like private corporations, non-profit organisations, and government entities are looking for skilled professionals who can keep their data and network safe. Thus, if you want to build a career in these industries, it is the best time to start.
DataSpace Academy has dedicated cybersecurity and
cyber forensics courses that can help you land better jobs in the future. These courses offer
An increasing number of cyberattacks is leaving organisations vulnerable. Organisations are looking for skilled cybersecurity and digital forensics experts who can help them safeguard their assets.
Although cybersecurity and digital forensics have distinct roles, they are closely intertwined. Both are essential parts of information security and are necessary for keeping your digital assets safe.
 Upto 50% Off on All CoursesValid till 15/07/2025
Upto 50% Off on All CoursesValid till 15/07/2025