Cybersecurity is fast becoming a booming sector in the modern digital-dependent era. With the ever-increasing cyber security incidents across the globe, the demand for skilled cybersecurity professionals will continue to grow beyond 2023. The cybersecurity sector is brimming with a huge volume of job roles worldwide - more than 3.5 million and counting. The great part is, that the cybersecurity industry offers lucrative packages as well; cybersecurity professionals can earn up to INR 15 LPA in the early stages of their careers. If you too want to be a part of this dynamic domain, you will need relevant skills and certifications. Also, you should build a solid portfolio containing cybersecurity projects. But, before proceeding further, you must know about the best Cybersecurity Projects for Portfolio.
Even if you have experience in this domain, a polished and updated portfolio can help land a job faster. A well-drafted cybersecurity portfolio could give you in-depth knowledge. You can work on multiple skill-developing projects for experience on the topic.
In this blog, you will get to know why building a cybersecurity portfolio is essential. Also, here are the top 7 cyber security projects you can make from scratch.
Anyone starting with these courses can accelerate their learning and develop new skills faster with suitable projects. Plus, projects give you hands-on experience in practising essential techniques, understanding cybersecurity fundamentals, and gaining experience. You can quickly get updated with vital cybersecurity skills like vulnerability assessment, threat detection, and Identity Access and Management governance.
Most cybersecurity and ethical hacking boot camps prefer project-based learning modules for teaching the most sought-after skills by recruiters. And, these projects show the recruiters that you possess the necessary skills required for a particular job. A career portfolio is an essential tool for any professional, especially someone in the cybersecurity field. A well-made portfolio can attract recruiters and help you land your dream job faster.

A career portfolio, containing all your best ethical hacking projects, can showcase your skills to potential employers. Most recruiters ask for a professional portfolio showcasing a candidate’s skills during the interview and screening process. Usually, a professional portfolio could contain samples of your work, visual demonstrations of your skills, and letters of recommendation from your professor, managers, and mentors.
And undoubtedly a glowing portfolio, containing a set of projects you have completed in the past, can distinguish you from others lining up for the interview. Need some help in setting up your portfolio or want to spice it up to attract recruiters? Here is a working guide to help you navigate through the process.
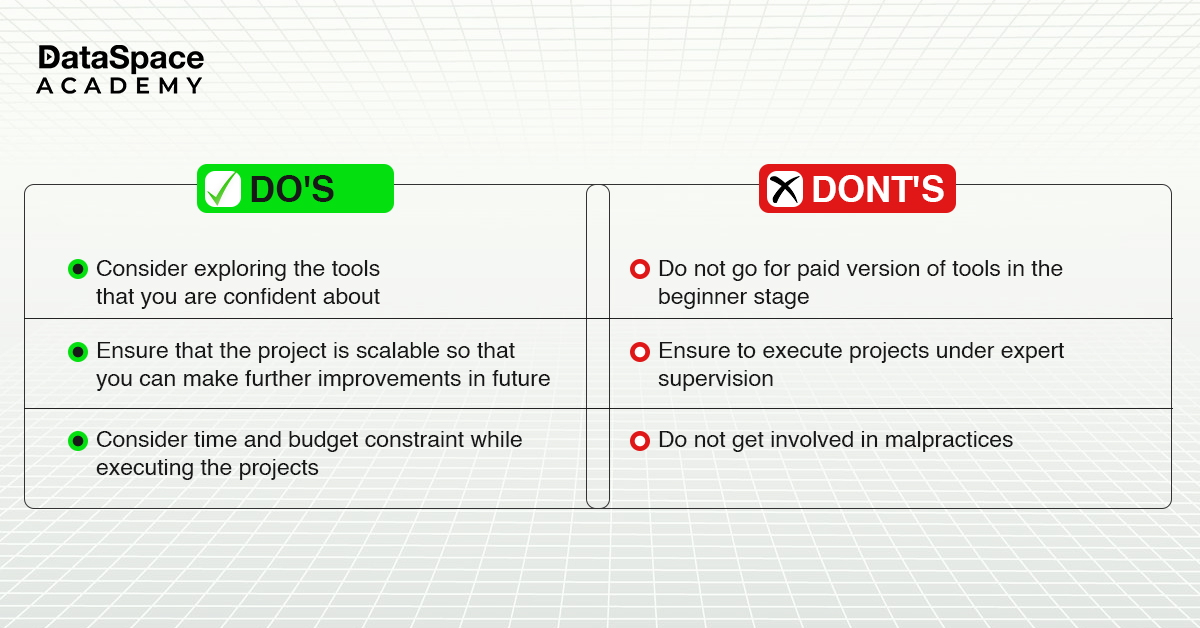
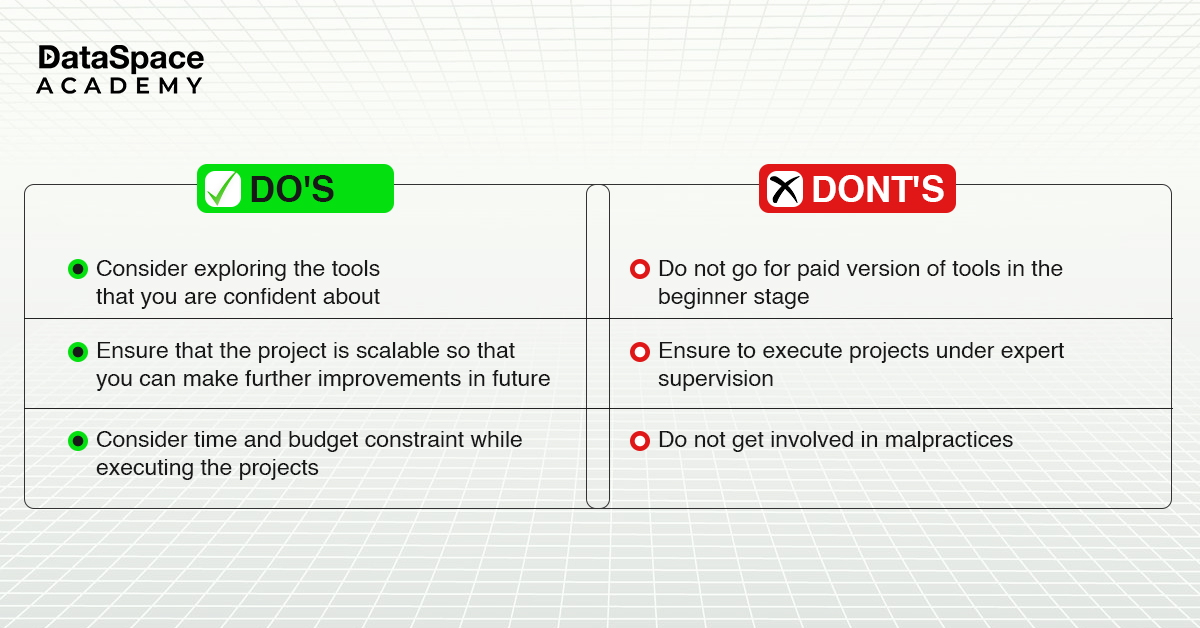
These tips can help you build a stellar ethical hacking portfolio for recruiters.
In cybersecurity hands-on experience is essential, and that’s where projects come in. When it comes to cybersecurity projects, there are a variety of options available. These projects let students learn key skills required the survive in the professional world.
Here are a few cyber security project topics that you can include in your portfolio:
-
In this project, you will simulate a cyberattack on a test network to identify existing vulnerabilities and weaknesses. You can use tools like Metasploit and Nessus to perform the testing. You can also recommend possible resolutions for fixing the issues as well.
-
Here you build an interface that protects computers within a network from malicious attacks and unauthorized access. This includes setting up authentication and authorization systems, implementing encryption, and monitoring application traffic.
-
Here, you will work on a malware sample, analysing its features, behaviours, and traits to determine potential methods for removal or mitigation.
-
In this project, you will build a cloud security interface that protects a mock cloud-based system and networks from unauthorized access. This includes setting up cloud security policies, implementing encryption, and monitoring cloud traffic.
-
Although an advanced-level project, it can give you immense learning exposure. Here, you build a mock user authentication portal with features such as signup and log-in/out. Additionally, you could incorporate multifactor authentication, facial recognition, and more into the portal as well.
-
This process is also named tirage and requires very sophisticated skills to collect the digital evidence of an incident. selection of tools to acquire the evidence also plays a key role as there are gigantic variety of tool kits available to attain identical results. Selecting the tool in accordance with the incident being responded to is always an influential and decisive element for successful acquisition.
-
Here the project goal is to build and deploy policy-centric, process and well-defined procedural-oriented activities to deal with any incident posed by the violation of approved policies in a forensically sound manner. The repetition of incident handling steps should yield identical results when and as attempted by another investigator or first responder.
These are just a few examples, but there are many other possibilities for cybersecurity projects depending on your interests and skills. The important thing is to demonstrate your ability to apply security concepts and tools in a practical setting while building free cybersecurity projects for portfolio.
There is an acute shortage of cybersecurity professionals across the globe. Corporate houses are always looking for ethical hackers who can safeguard their enterprise network against potential digital threats. Anyone willing to learn the essential hacking skills can seamlessly land a lucrative job in these corporate houses. Working on these projects and building your work portfolio would help recruiters find you more easily.
Dataspace Academy is running the best
ethical hacking and network security training courses in Kolkata. In these courses, you can learn more about the latest tools and skills demanded by ethical hacking recruiters across industries. Plus, the trainers help you build cybersecurity-related projects that can strengthen your portfolio.
 Upto 50% Off on All CoursesValid till 15/07/2025
Upto 50% Off on All CoursesValid till 15/07/2025