Can your palm prints reveal your destiny? Maybe Yes or No but definitely something more tangible- your identity.
We are talking about
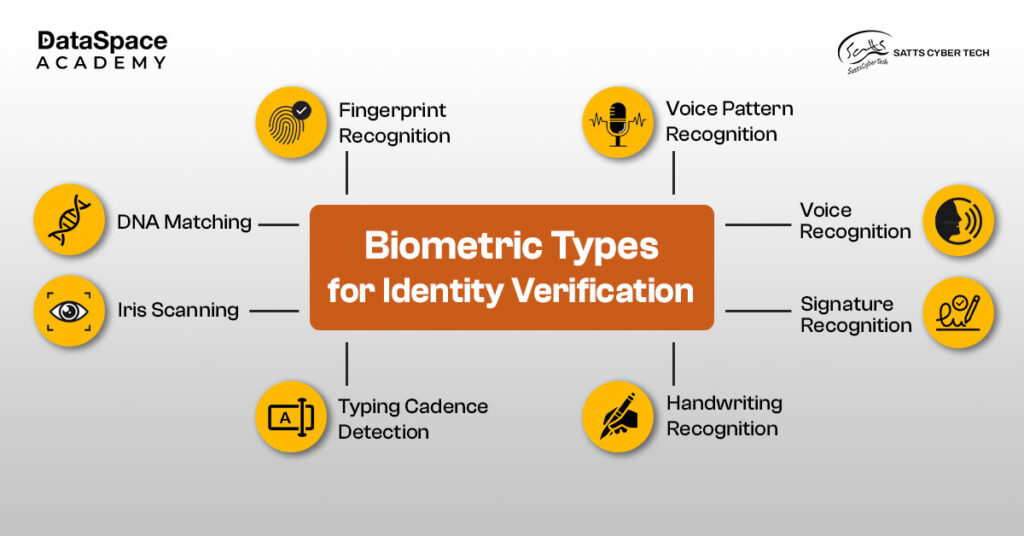
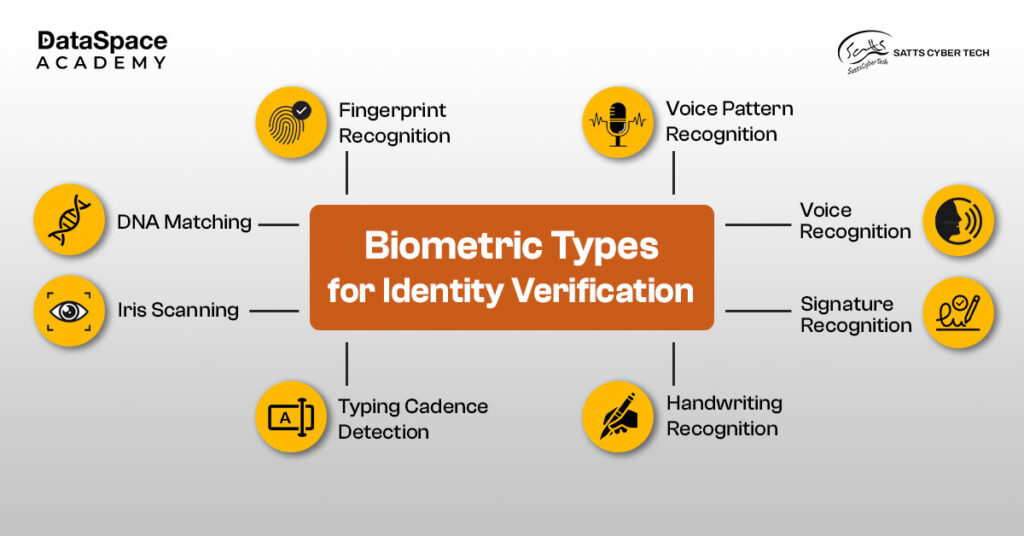
biometric security, probably, the most dependable security barrier that leverages what is uniquely yours - like your fingerprints, face scan, iris pattern, or voice. The term ‘biometric’ is derived from two Greek words Bio (life) and Metric (measure). Together, the term means assessing a user’s biological traits as a unique security authentication factor. This particular factor is all set to fuel the global
biometric market which is projected to reach $83 billion by 2028, reflecting its growing adoption. Let’s unfold more in this insightful read.
Biometric security is all about verifying your (users) unique physical characteristics - such as fingerprints, palm prints, facial scans, iris pattern, and voice - to grant access to a protected place. A
biometric security system uses the data gathered as immutable defense against advanced cyber attacks. Additionally, innovations like 3D mapping in facial recognitions and multi-spectral imaging have heightened the accuracy and reliability of biometric as the new standard of security authentication.
A common example of biometric authentication is unlocking your phone and apps with touch IDs like fingerprints or face scans. Then, office check-ins with your fingerprints on biometric systems is another popular example of biometric security scan.
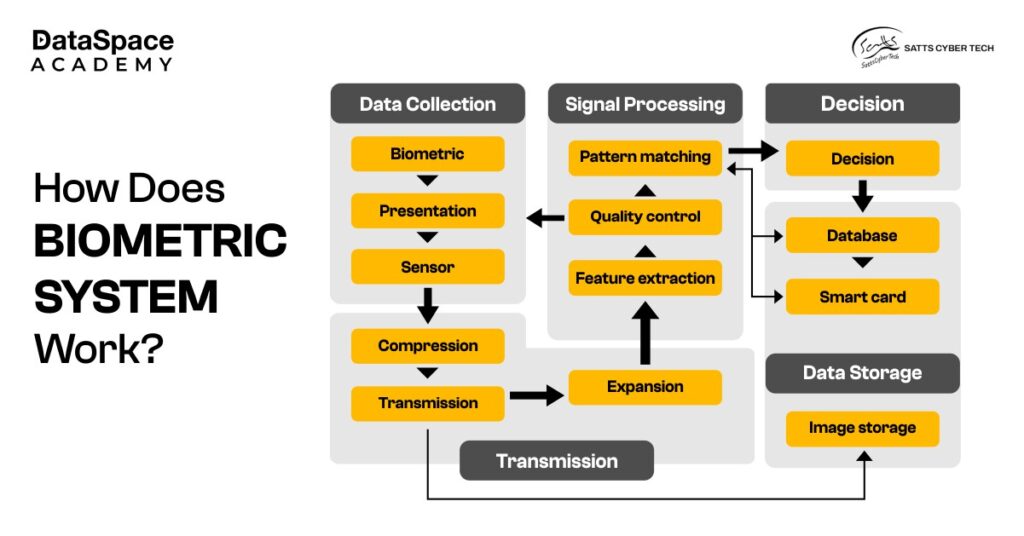
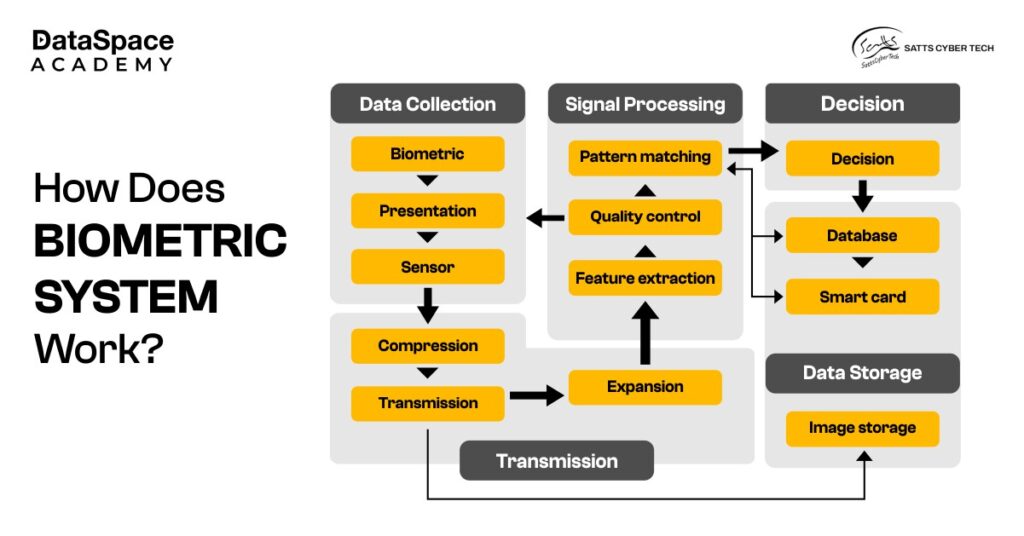
The entire mechanism of
biometric authentication systems is based on constant capturing of biometric data, and comparison with a saved database - to find a match. If the collected data matches the saved database, the biometric system will grant secure access.
All biometric systems are equipped with 3 basic components such as:
Presenting a brief synopsis on how your physical data is processed by the
biometric access control system
 Biometric security technology
Biometric security technology has become a cornerstone of digital security and convenience in the modern world. With the growing need for impenetrable defense systems, the significance of biometric security systems has become more vital than ever.
Biometric security is a game-changer in safeguarding your personal data with your physical data. However, understanding its nuances is crucial to ensure 100% protection. If you're passionate about enhancing security skills, consider a
cybersecurity certification for beginners - a perfect starting point to navigate and secure a desirable job role in the evolving digital landscape. On a final note, always treat your biometric details as precious as your financial information.

 Upto 50% Off on All CoursesValid till 15/07/2025
Upto 50% Off on All CoursesValid till 15/07/2025