“About seven out of 10 Indian consumers have faced tech support related scams” (Source: outlookindia.com).
Modern cybercriminals have grown smarter in finding innovative ways to exploit network and application vulnerabilities, leaving organisations in huge losses and slowing down the overall national GDP. No country, industry, or individual is immune to cyber risks, and no government agency, company, or individual can thwart risks alone. After all, cybersecurity is a team sport. The government and law enforcement agencies are actively looking for experts in the cybersecurity field - someone who can proficiently respond to the eminent cases of cybercrimes.
Private and government organisations are under constant pressure to find the right expert to react quickly to the exponentially increasing number of cybersecurity threats. They are actively hiring skilled cybersecurity professionals who can streamline investigations and secure digital warehouses. Also, law enforcement agencies are launching specialised cybersecurity wings for aiding cybercrime victims.
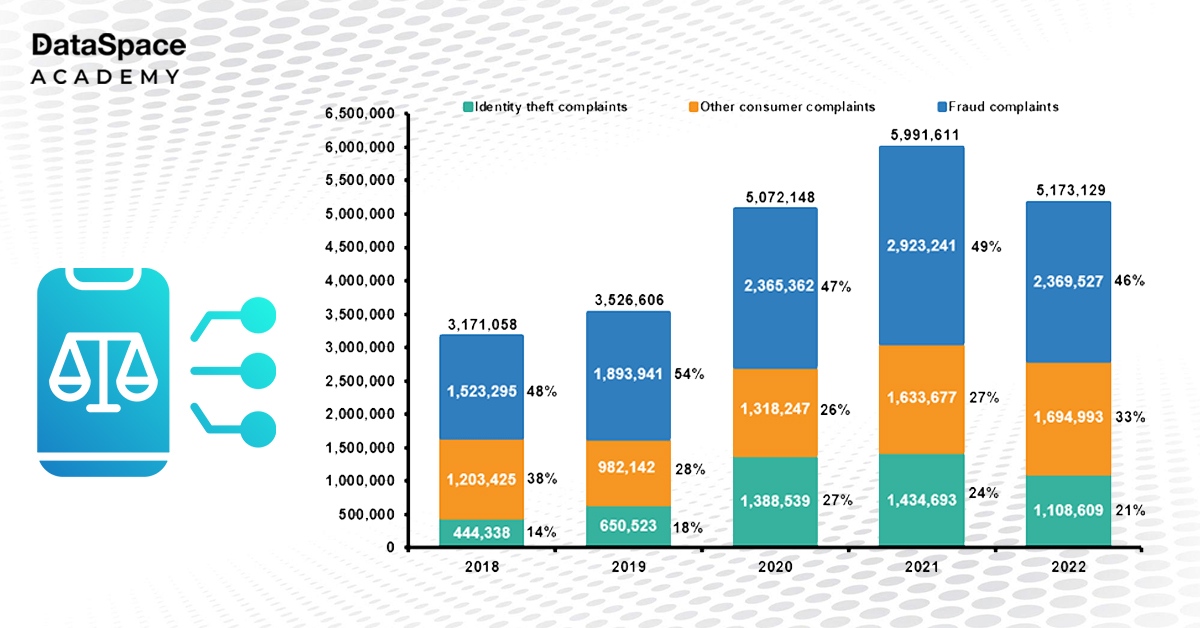
Cybercriminals are using advanced methods to hack into our computers as technology progresses. It is a growing concern and challenge for law enforcement agencies. They are trying to proactively locate and neutralise these threats while promoting safer online behaviour. In the contemporary age of constant digitization, cybercrime is one of the most alarming crimes all across the world.
Cybersecurity and raising awareness about cybercrimes are becoming essential for law enforcement agencies. These agencies are taking initiatives to improve their response rates towards cybercrimes, streamline investigations, and secure digital warehouses for storing pieces of evidence for the future. As mentioned above, specialised cybersecurity wings are being launched for helping cybercrime victims. The government is also encouraging law enforcement officers to take up cybersecurity education and certifications to better help the victims.
And since cybersecurity is a growing domain, with 3.5 million unfilled positions (Source: cybersecurityventures.com) and growing, these professionals can seamlessly switch to more high-paying roles in the future. According to AmbitionBox, a security engineer with three to four years of experience can earn close to ₹ 15 to 19 LPA.
Law enforcement professionals hold the skills and temperament to transition to the cybersecurity sector. These officials are trained in situational awareness, problem-solving skills, and swift intel collection. They are also updated about compliance with security protocols. These skills are high in demand in the cybersecurity sector as this domain needs intelligent threat analysis and quick redressal to internet security situations. Moreover, law enforcement professionals have taken the oath to fight crimes and make the world a safer place.
Alongside this, a professional transitioning to the cybersecurity sector should hold basic familiarity with technology and a deep understanding of hacking incidents and types. A strong foundation in networking, computer systems, and programming languages is essential. Overall, the ability to adapt quickly to new technologies and stay up-to-date on the latest security trends and techniques are crucial for success in this field.
Currently, cybersecurity is one of the biggest job generators across the globe. The career transition from law enforcement to cybersecurity roles follows an exciting roadmap.
A professional switching to cybersecurity from another career background (especially non-IT) would need to start with a foundational course such as CompTIA Security+ or Certified Ethical Hacker (CEH). Once they are done with these courses, they can proceed to advanced specialities for skill building.
Apart from theoretical knowledge, these candidates have to spend time working on platforms like HackTheBox, TryHackMe, or AttackDefense for practical experience.
Here is a detailed roadmap for building a career in cybersecurity:
-
Foundation courses work as a stepping stone for understanding the basics of cybersecurity. These programs help candidates differentiate between different types of attacks, methods used by hackers to infiltrate the system, and several defence methodologies for protecting the system.
-
Valid, industry-relevant certifications validate a candidate’s skills. They provide credibility to the candidate and demonstrate their hold over the subject to potential employers. Some early-level certifications include Certification In Ethical Hacking, Certified Ethical Hacker (CEH), and Cyber Security Essential Program.
-
Once done with the fundamentals, the candidate can switch to more specializations in cybersecurity such as Certification in Cyberforensics, incident response, or pen-testing for security engineers.
-
In cybersecurity, apart from theoretical knowledge, practical experience is critical for success. Candidates can work on TryHackMe, free Dataspace Academy Labs, or AttackDefense for practical skills. These labs offer candidates exposure to hands-on, participative learning training.
Once a candidate has gained relevant experience and skills, it's time to look for entry-level cybersecurity roles or internships. A relevant cybersecurity resume- rich in industry-related words- could be immensely helpful in the job pursuit. According to experts, networking with professionals in the domain will help them stay up-to-date with the current industry trends.
Transitioning from law enforcement to a career in cybersecurity can be challenging but rewarding. Most law enforcement personnel start off with entry-level courses, followed by mid-level and advanced-level roles with experience.
Summing up, there is a huge demand for cybersecurity professionals - especially in law enforcement agencies and private organisations. Cybersecurity is a dynamic and evolving field, extending highly potential job opportunities with generous pay packages. If you are a law enforcement official planning to switch to another domain, a career in cybersecurity would be highly rewarding.
Aspiring to transition to a cybersecurity career? DataSpace Academy is there to help you.
 Upto 50% Off on All CoursesValid till 15/07/2025
Upto 50% Off on All CoursesValid till 15/07/2025