Cybersecurity is an in-demand field with a 0% unemployment rate. In reality, as of now, over half a million cybersecurity professionals are required in India (Source: Statista.com). And according to experts, these numbers will only rise in the future. However, most professionals cannot make a successful transition to a career in cybersecurity. Why? Lack of necessary hands-on skills and experience could be among the top reasons. However, there is a severe talent shortage in the industry.
Companies are actively hiring cybersecurity professionals for protecting their sensitive data and managing their networks. And they are willing to pay high salaries to the right talent. The high demand and better pay in the sector have been attracting professionals from other backgrounds as well, such as the general IT professionals.
The twin advantages of high salary and long-term job security is a major inspiration for several IT professionals contemplating a switch to cybersecurity. Plus, both fields are closely related and require overlapping skills. Most IT professionals pick up relevant cyber security certification courses according to their skill set before transitioning into this domain. But would it (cybersecurity) be a wise career choice?

Cybersecurity is one of the most in-demand careers, primarily due to the exponentially growing number of cybercrimes today. Cybersecurity professionals play an important role in protecting the company and its sensitive data from cyberattacks and other prominent threats. They have coveted resources of an organization and are one of the highest-paid resources.
Since 2016, the unemployment rate for cybersecurity has remained at 0% (source:cybersecurityventures.com). And not surprisingly, the talent gap is widening day by day. The global cybersecurity workforce shortage would reach up to 3.5 million by 2025 (Source: economictimes.com).
Candidates switching to cybersecurity are greeted with high-paying wages, flexible working hours, and future career growth. Plus, there is never a dull moment in this domain. There is always a chance of learning new things, exploring new industries, and upskilling themselves.
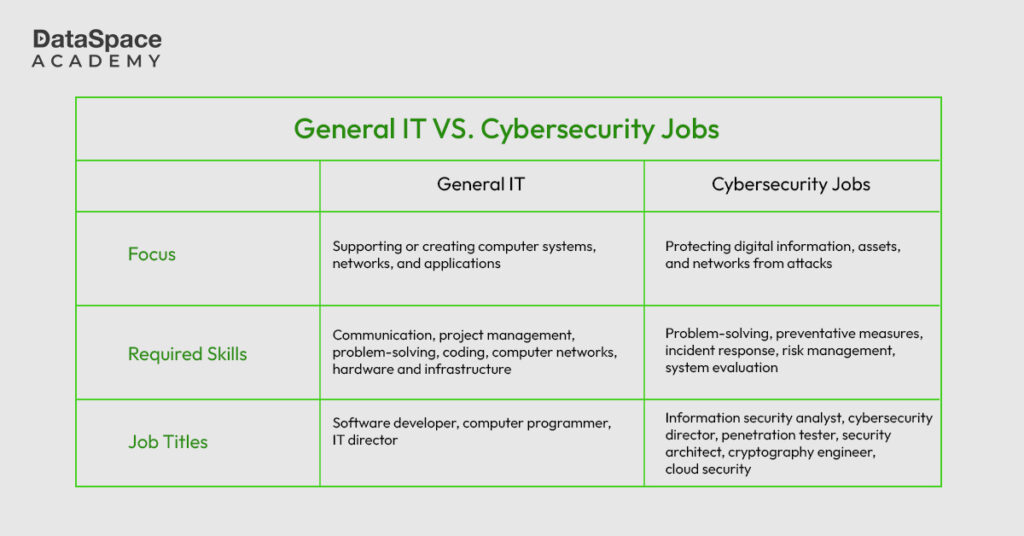
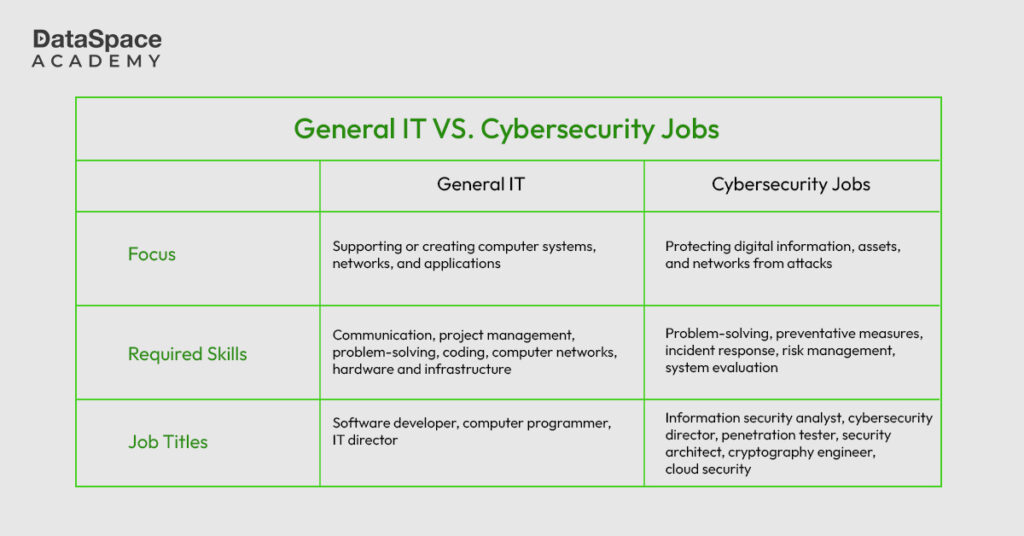
Cybersecurity is a dynamic, in-demand field attracting professionals from different domains including information technology. Not surprisingly, General IT and cybersecurity roles overlap each other. In fact, cybersecurity is often considered a specialised subfield within IT security. Both IT and cybersecurity professionals perform networking and coding responsibilities, database management, and perform system configuration and administration. But to a varying degree.
The primary focus of a cybersecurity professional is to protect the databases, network, and operating systems from outside and inside attacks, whereas General IT employees aim for functionality within the system and user experience above all else. The General IT roles involve managing and maintaining data and information generated by the organisation. It could include both online and offline assets. On the other hand, cybersecurity roles focus on preventing and protecting data and information from outside and inside threats. Its prime motive is to neutralise threats that originate online.
Building a career in cybersecurity is highly rewarding. Anyone can transition into cybersecurity from any domain, but IT professionals always have an obvious advantage given their background in tech. Learners willing to make a transition from General IT need to learn cybersecurity and other essential skills.
Here is a career transition roadmap for someone willing to make a switch to cybersecurity from General IT.
-
There are multiple cyber security courses online and offline that can help you transition into cybersecurity from General IT. These programs explore a learner’s area of interest and offer the high-quality training and flexibility required to take the career to the next level. Some of the popular cyber security certification courses are -
-
Since cybersecurity is a vast domain with multiple branches and specialisations, the learners can opt for opportunities that fit their niche. Ideally, someone transitioning from IT should choose a cybersecurity specialisation that is closely related to their current role. These specialisations smoothen the career transition and help in successfully landing a rewarding job in cybersecurity.
-
Along with working on certifications, gathering relevant hands-on experience in real-world scenarios is essential. Hands-on experience helps learners understand their knowledge gaps and strengthen their strong points. For a hands-on experience, the learner can participate in internships or work on security-related projects, participate in bug bounty programs or hackathons, or contribute to open-source security tools to showcase their merit. DataSpace Academy offers free practice labs for learners who are starting with cyber security.
-
Networking with cohorts and experienced professionals helps with gaining valuable insights about the industry and how it operates. Professionals transitioning into cybersecurity could attend conferences, meetups, and other networking events to build their personal network within the cybersecurity industry.
Moving from information technology to cybersecurity is relatively easier. Both fields overlap, meaning you’ll already have core skills that you can refine.
General IT professionals can transition well into mid-level and advanced-level cybersecurity roles with relevant years of experience. Here are some of the job roles they can take up in the cybersecurity field.
Cybersecurity is a dynamic field that aims to make the virtual world more secure and guarded in the era of rising cyber crimes. Anyone switching from an IT career to cybersecurity will find it exciting and exhilarating. Often general IT and cybersecurity domains cross paths and overlap, making it easier for professionals to make a switch between the two domains. If you are aiming to make a switch into the domain, Dataspace Academy has cybersecurity basics and advanced-level career-building courses to help you make a successful transition.
Dataspace Academy is ready to build your career in cybersecurity you.